How To Configure DNS (BIND) Server on Red Hat Enterprise Linux 7
Updated: Oct 3, 2021
Previously, we have explained "How DNS or Name Resolution Service Work". today let's do the DNS configuration on on Red Hat Enterprise Linux 7.
Step:1 To install DNS (BIND) server required packages.
# yum -y install bind bind-utilsStep:2 To configure BIND to listen on a IP addresses and will allow clients from the mentioned network can query the DNS for the name to ip translation.
# vi /etc/named.conf
//
// named.conf
//
// Provided by Red Hat bind package to configure the ISC BIND named(8) DNS
// server as a caching only nameserver (as a localhost DNS resolver only).
//
// See /usr/share/doc/bind*/sample/ for example named configuration files.
//
// See the BIND Administrator's Reference Manual (ARM) for details about the
// configuration located in /usr/share/doc/bind-{version}/Bv9ARM.html
acl my-host { 192.168.122.144; };
acl my-net { 192.168.122.0/24; };
options {
listen-on port 53 { 127.0.0.1; my-host; };
listen-on-v6 port 53 { ::1; };
directory "/var/named";
dump-file "/var/named/data/cache_dump.db";
statistics-file "/var/named/data/named_stats.txt";
memstatistics-file "/var/named/data/named_mem_stats.txt";
recursing-file "/var/named/data/named.recursing";
secroots-file "/var/named/data/named.secroots";
allow-query { localhost; my-net; };
/*
- If you are building an AUTHORITATIVE DNS server, do NOT enable recursion.
- If you are building a RECURSIVE (caching) DNS server, you need to enable
recursion.
- If your recursive DNS server has a public IP address, you MUST enable access
control to limit queries to your legitimate users. Failing to do so will
cause your server to become part of large scale DNS amplification
attacks. Implementing BCP38 within your network would greatly
reduce such attack surface
*/
recursion yes;
dnssec-enable yes;
dnssec-validation yes;
/* Path to ISC DLV key */
bindkeys-file "/etc/named.iscdlv.key";
managed-keys-directory "/var/named/dynamic";
pid-file "/run/named/named.pid";
session-keyfile "/run/named/session.key";
};
logging {
channel default_debug {
file "data/named.run";
severity dynamic;
};
};
zone "." IN {
type hint;
file "named.ca";
};
include "/etc/named.rfc1912.zones";
include "/etc/named.root.key";Note: we can verify the configuration file by running this command
# named-checkconf /etc/named.conf
And the output should be none, if all good to go.
Step:3 To create zones entry, the forward zone entry for the example.com domain and the reverse zone entry for the IP network.
# vi /etc/named.rfc1912.zones
// named.rfc1912.zones:
//
// Provided by Red Hat caching-nameserver package
//
// ISC BIND named zone configuration for zones recommended by
// RFC 1912 section 4.1 : localhost TLDs and address zones
// and http://www.ietf.org/internet-drafts/draft-ietf-dnsop-default-local-zones-02.txt
// (c)2007 R W Franks
//
// See /usr/share/doc/bind*/sample/ for example named configuration files.
//
zone "localhost.localdomain" IN {
type master;
file "named.localhost";
allow-update { none; };
};
zone "localhost" IN {
type master;
file "named.localhost";
allow-update { none; };
};
zone "1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.ip6.arpa" IN {
type master;
file "named.loopback";
allow-update { none; };
};
zone "1.0.0.127.in-addr.arpa" IN {
type master;
file "named.loopback";
allow-update { none; };
};
zone "0.in-addr.arpa" IN {
type master;
file "named.empty";
allow-update { none; };
};
# the forward zone entry for the example.com
zone "example.com" IN {
type master;
file "named.example.com";
allow-update { none; };
};
# the reverse zone entry for the 192.168.122.0/24 network.
zone "122.168.192.in-addr.arpa" IN {
type master;
file "named.122.168.192";
allow-update { none; };
};Step:4 To create forward and reverse lookup files (zone database files) under /var/named/ directory.
# cp /var/named/named.localhost /var/named/named.example.com
# cp /var/named/named.loopback /var/named/named.122.168.192
# vi /var/named/named.example.com
$TTL 1D
@ IN SOA dns1.example.com. root.dns1.example.com. (
1000 ; serial
1D ; refresh
1H ; retry
1W ; expire
3H ) ; minimum
;Name Server Information
@ NS dns1.example.com.
@ IN A 192.168.122.144
;IP address of Name Server
dns1 IN A 192.168.122.144
;Mail exchanger
example.com. IN MX 10 mail.example.com.
;A - Record HostName To IP Address
www IN A 192.168.122.180
mail IN A 192.168.122.200
;CNAME record
ftp IN CNAME www.example.com.
# vi /var/named/named.122.168.192
$TTL 1D
@ IN SOA dns1.example.com. root.dns1.example.com. (
1000 ; serial
1D ; refresh
1H ; retry
1W ; expire
3H ) ; minimum
@ IN NS dns1.example.com.
;Reverse lookup for Name Server
155 IN PTR dns1.example.com.
;PTR Record IP address to HostName
180 IN PTR www.example.com.
200 IN PTR mail.example.com.
# chgrp named /var/named/named.*Note: we can check our zone database files as below:
# named-checkzone example.com /var/named/named.example.com
zone example.com/IN: loaded serial 1000
OK
# named-checkzone 122.168.192 /var/named/named.122.168.192
zone 122.168.192/IN: loaded serial 1000
OK
and make sure, whenever we update the zone lookup file, we need to change/increment the serial like 1001 ;Serial
Step:5 To start and enable bind(named) service on system startup.
# systemctl status named
# systemctl enable named
Created symlink from /etc/systemd/system/multi-user.target.wants/named.service to /usr/lib/systemd/system/named.service.Step:6 If Firewalld service enabled and running, need to allow rule in the firewall to let clients can connect to the DNS server for name resolution.
# firewall-cmd --permanent --add-port=53/udp
# firewall-cmd --reloadStep:7 To verify the DNS server name resolution from the client system.
DNS Client configuration at the client system:
1. we can add add a DNS server ip address in /etc/resolv.conf in client and do not required any services restart.
# vi /etc/resolv.conf
# Generated by NetworkManager
search example.com
domain example.com
nameserver 192.168.122.1442. If Network Manager is managing the networking in the client system then need to add following entry in /etc/sysconfig/network-scripts/ifcfg-eXX file. and restart the NetworkManager service.
# vim /etc/sysconfig/network-scripts/ifcfg-eth0
:::::::::::: CUT SOME OUTPUT :::::::::::::
DNS1=192.168.122.144
:::::::::::: CUT SOME OUTPUT ::::::::::::: Using nslookup command for DNS query:
# nslookup
> set type=mx
> example.com
Server: 192.168.122.144
Address: 192.168.122.144#53
example.com mail exchanger = 10 mail.example.com.
> set type=ns
> example.com
Server: 192.168.122.144
Address: 192.168.122.144#53
example.com nameserver = dns1.example.com.Using dig command for DNS query:
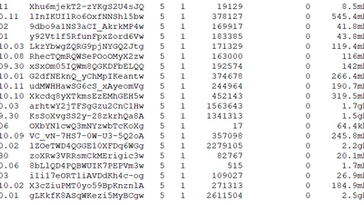
# dig -x 192.168.122.180
; <<>> DiG 9.11.4-P2-RedHat-9.11.4-16.P2.el7_8.6 <<>> -x 192.168.122.180
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 45761
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 2
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags:; udp: 4096
;; QUESTION SECTION:
;180.122.168.192.in-addr.arpa. IN PTR
;; ANSWER SECTION:
180.122.168.192.in-addr.arpa. 86400 IN PTR www.example.com.
;; AUTHORITY SECTION:
122.168.192.in-addr.arpa. 86400 IN NS dns1.example.com.
;; ADDITIONAL SECTION:
dns1.example.com. 86400 IN A 192.168.122.144
;; Query time: 0 msec
;; SERVER: 192.168.122.144#53(192.168.122.144)
;; WHEN: Sat Jul 25 15:21:20 +08 2020
;; MSG SIZE rcvd: 121My DNS server has the internet connectivity and the recursion yes; (by default) has been configured, we can try the Non-authoritative DNS query, as below:
# nslookup www.jazakallah.info
Server: 192.168.122.144
Address: 192.168.122.144#53
Non-authoritative answer:
www.jazakallah.info canonical name = www59.wixdns.net.
www59.wixdns.net canonical name = balancer.wixdns.net.
Name: balancer.wixdns.net
Address: 35.247.167.166DNS lookup answer is Non-authoritative, Because, there is no jazakallah.info domain information in my zone database files, and this reply is coming from remote DNS servers (35.247.167.166).





Comments